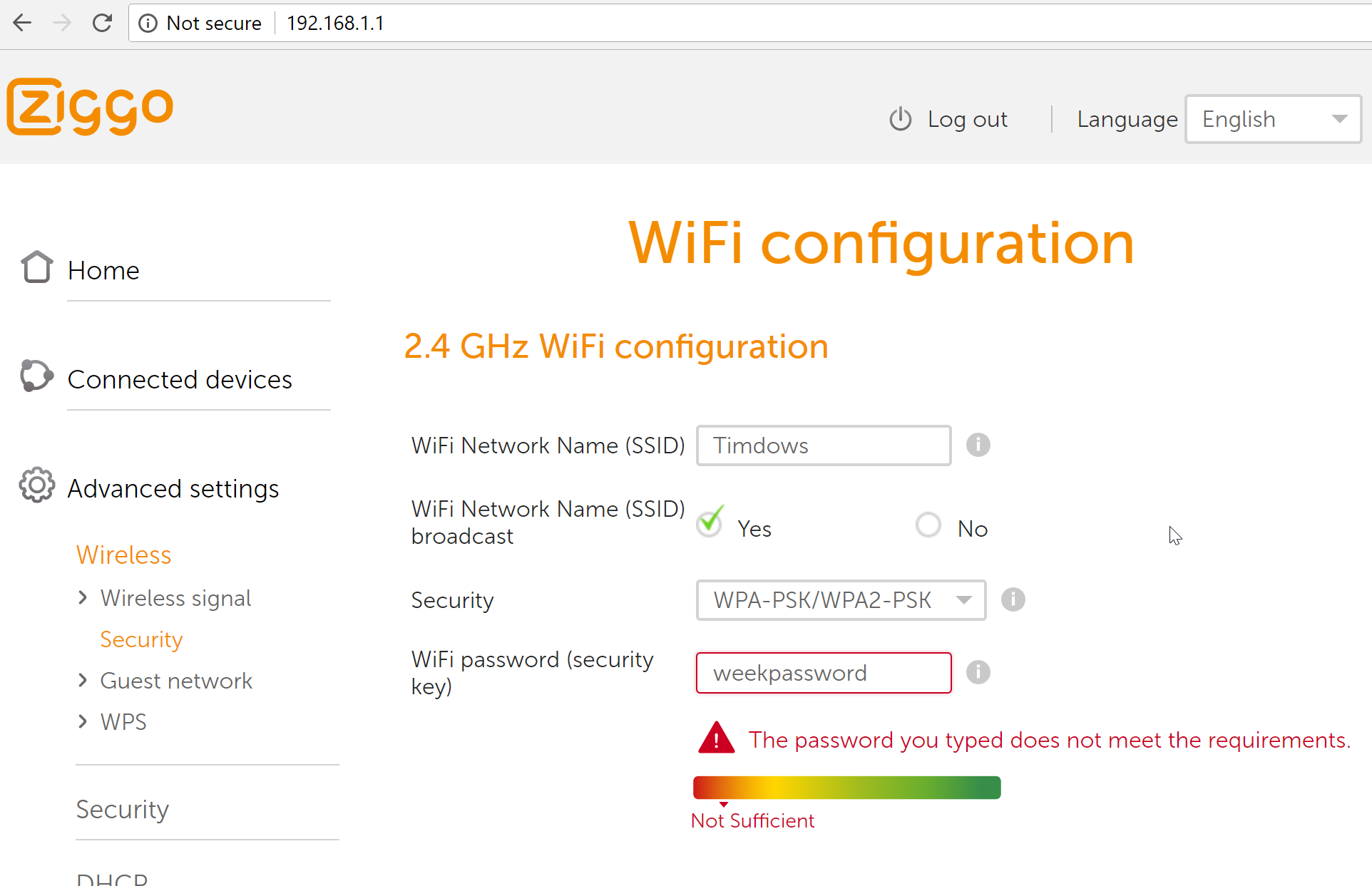
My local ISP, Ziggo, uses a stupid way to force using a strong WiFi password. First of all, I want to be in control of the password, I can set the security to none, but if I want to use WPA2 the system forces me to pick a password with 10 characters and 3 other restrictions.
The device I have is a Ziggo Connectbox, on the support website they incidate that on avarage users change their password in 10 minutes.
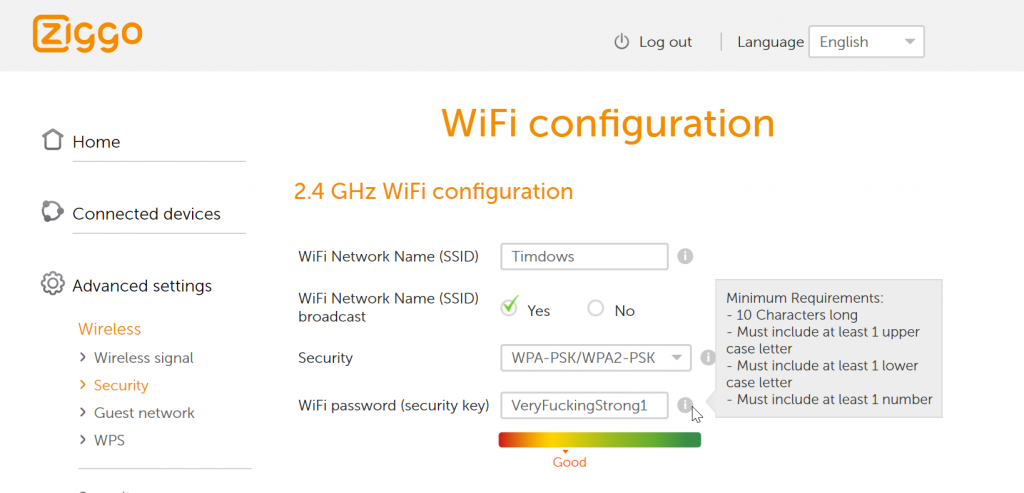
I want to use a password that does not meet these requirements, just because, so the game is on to trick the system in accepting my “weakpassword”.
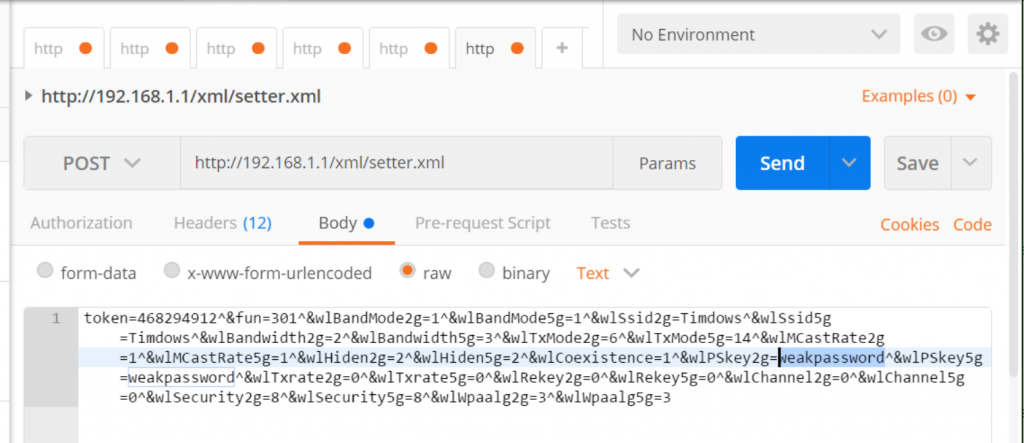
Option 1: Replay XHR
After succesfully changing the WiFI configuration, I was able to capture the XHR and copy it to Postman.
I had to change:
- token in the body
- password (for 2.4G and 5G) in the body
- cookie SID and cookie sessionToken values in the headers
Option 2: Change javascript values
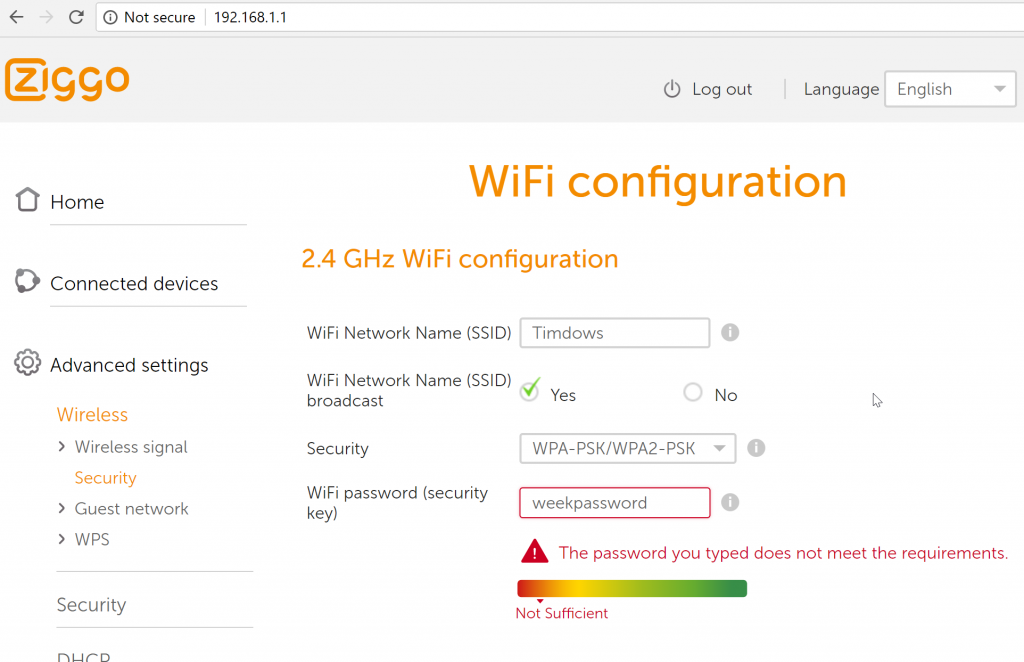
With the previous option, I was sure that there was no server side checking of the input values (Do Not Trust User Input Directly dear programmers of this configuration page).
Using Chrome I was albe to get the called function that checks the password strength, by setting a breakpoint the callstack was made visible, and by setting a breakpoint just before the check took place, I could update the javascript values and trick the function in accepting my weak password.
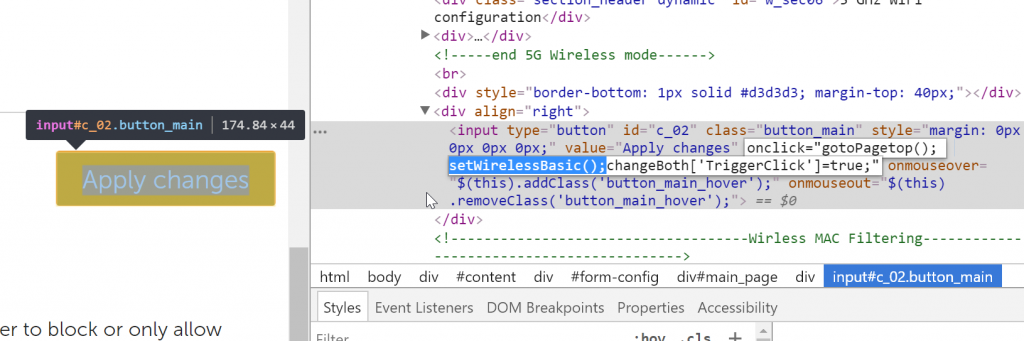
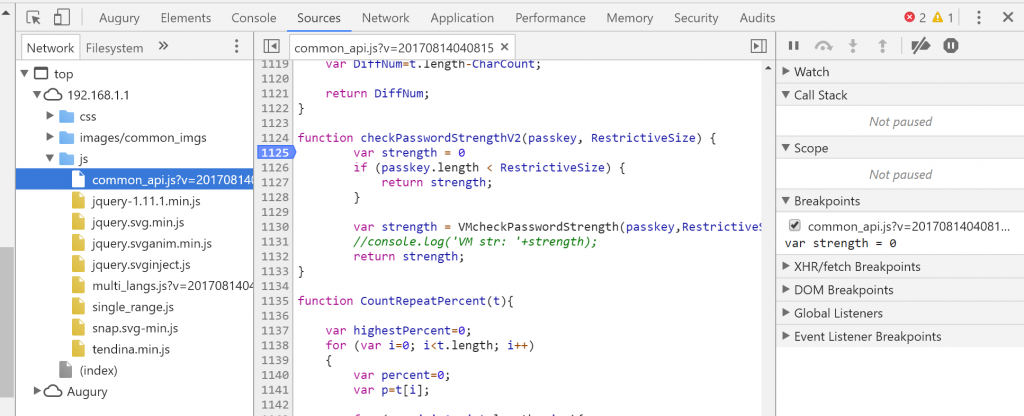
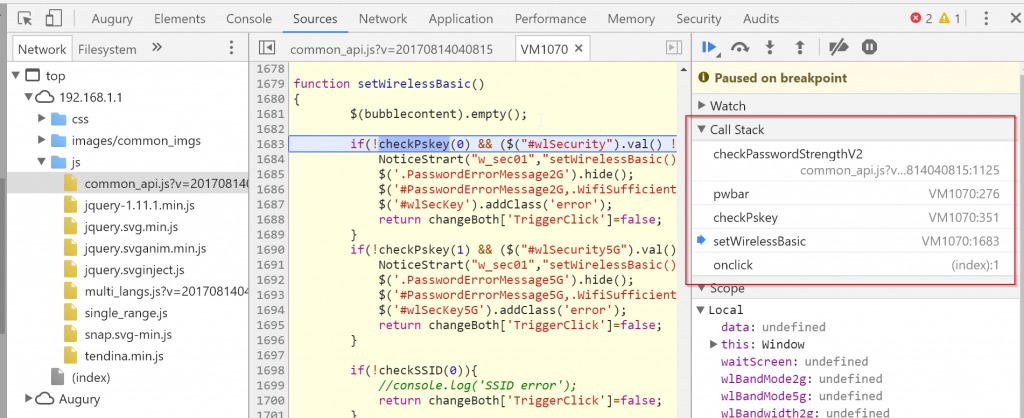
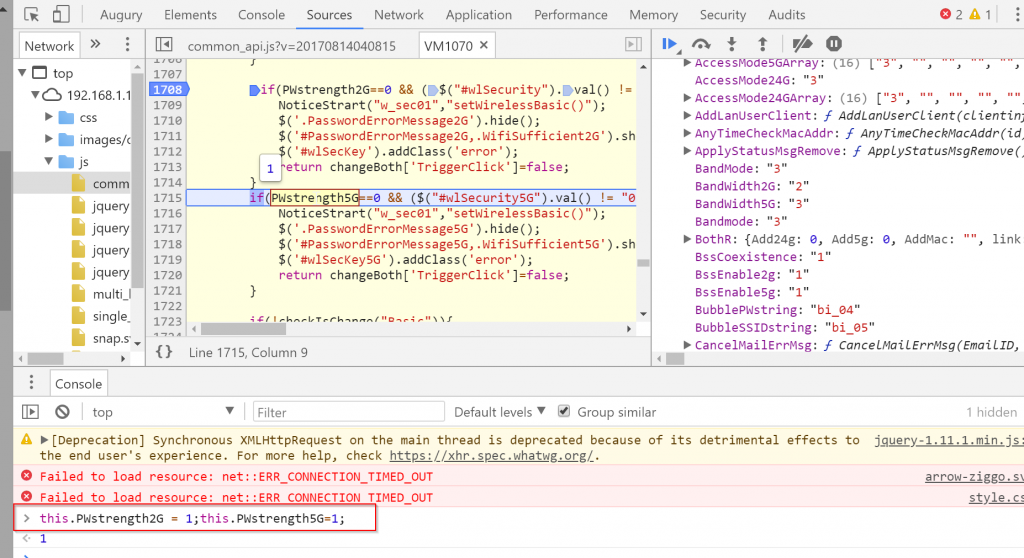
The executed code
[code lang=”js”]this.PWstrength2G = 1;this.PWstrength5G = 1;[/code]
Conclusion
The user input on this form was not checked by the device itself, it relied a 100% on the javascript checks.
It feels dumb that I can disable the WiFi security but if I want to enable it, this stupid password restriction come with it.
Writing this blog took longer than the action itself, I hope someone does benefit from it.
Ziggo, allow users to pick their own password and make sure that user forms are also checked by the device when submitted.
Thanks for sharing! Saved me some time.
I agree the password restrictions are really stupid. I’m happy the password requirements are only checked client side.