What is it? 
The guys from https://ngrok.com have done some great work. Their slogan:
I want to expose a local server behind a NAT or firewall to the internet.
Don’t constantly redeploy your in-progress work to get feedback from clients. ngrok creates a secure public URL (https://yourapp.ngrok.io) to a local webserver on your machine.
So I wanted to test this for a while, and now that I did, wow it is incredible what they have created.
The demo
I wanted to show my colleague some progress I have made on a web application.
Of course, even my local development environment uses https, so I ran the following command:

But to bad, I need a Pro or Business account to support TLS

Luckaly my application also supports oldish http traffic over port 5005.
Just run the following command:
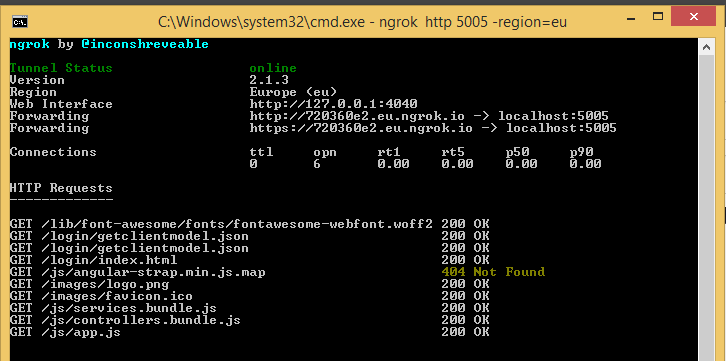
ngrok http 5005 -region=eu
Some web applications give an error if an other host header is present. This can be solved with the following command
ngrok http [port] -host-header="localhost:[port]"
After I went to my assigned webpage, I got the login screen, being served from my ASP.NET Core application running on my laptop in debug mode.

All requests are now served via this tunnel, and my colleague could visit my web application, and still login with an on-premises test ActiveDirectory account to make sure we had some wow effect there.

Introspect all of the HTTP traffic
The ngrok application creates a simple webpage that uses websockets to push information about the traffic to it.
On this webpage you can see some configuration values and metrics.
And on the inspect page you can see all get and post information and even resend it with the replay button


Comments are closed.